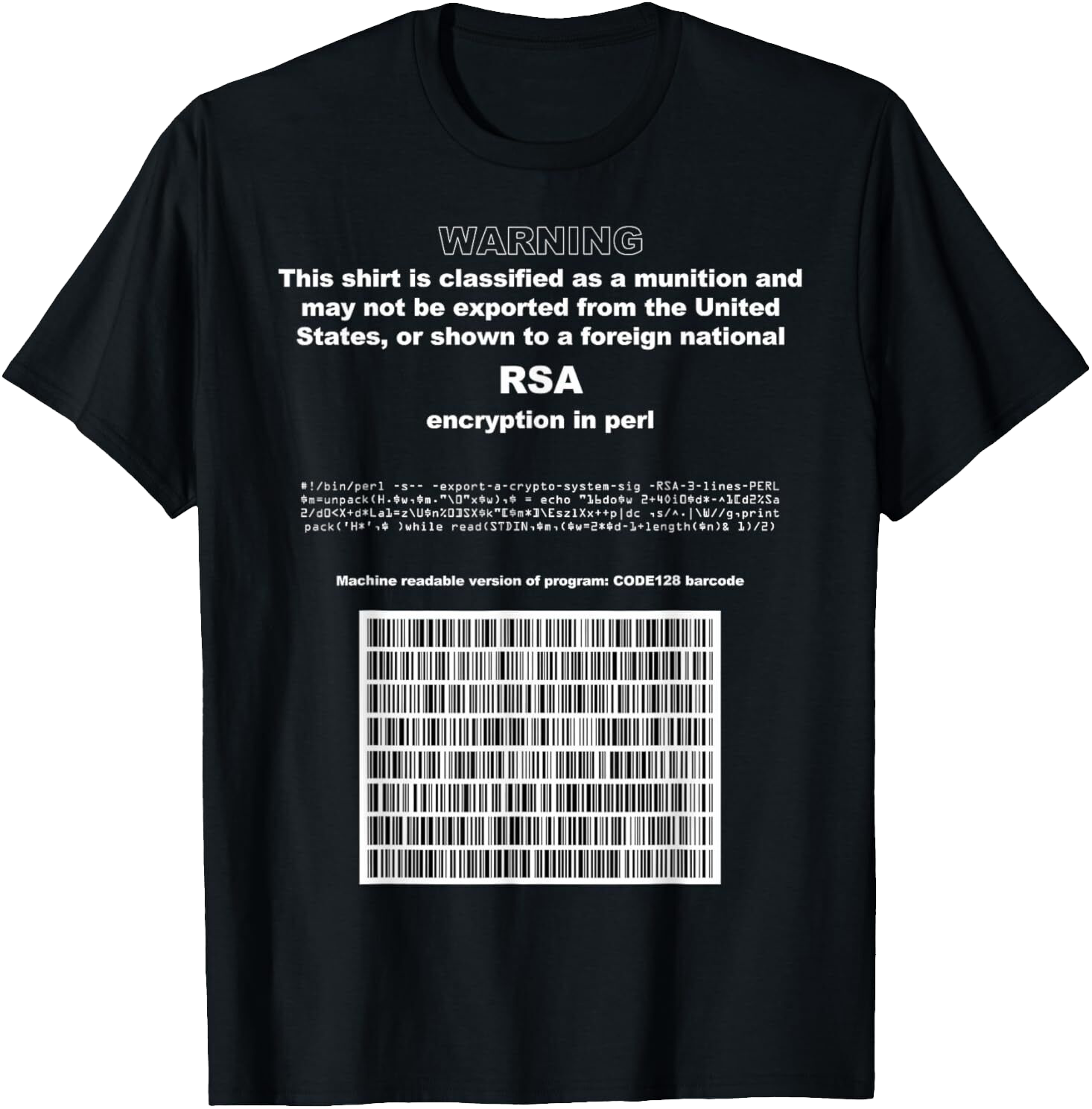
The source code for the RSA encryption algorithm printed on a T-shirt, one version of the Perl RSA “munition” T-shirt, by Adam Back, 1995.
The idea of printing the RSA code on a shirt – a process dubbed “T-shirtization” – was proposed by Joel Furr, but this code has also been reproduced in various other forms, for example as a tattoo, as expressions of the struggle for the liberalization of cryptography.
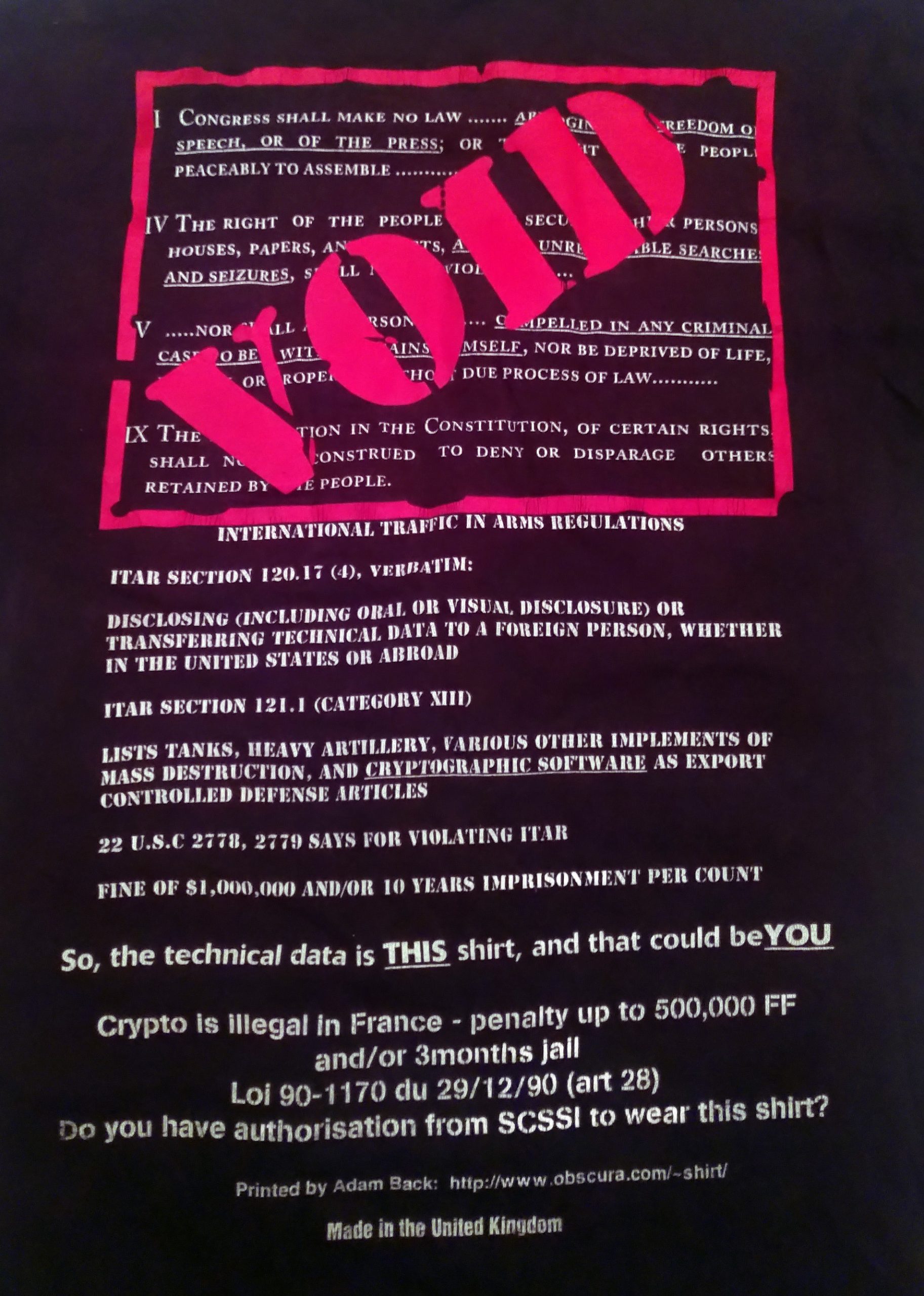
On the back of the French adaptation of the T-Shirt, the inscription at the bottom refers to the French law of the time and to the SCSSI – Central Service for Information Systems Security, one of the predecessors of the current ANSSI – National Cybersecurity Agency of France.
ABOUT CODE
Source code can be considered by some as illegal in itself. In the aftermath of World War II, the United States adopted a very restrictive policy on the use and export of encryption techniques. At the height of the Crypto Wars – the battle for the liberalization of encryption – in the early 1990s, cypherpunks developed this implementation of the RSA encryption algorithm in the Perl language.
Fitting within a few lines, the RSA encryption could be widely shared, notably printed on a T-shirt. The aim is both to troll the government and to point out the inconsistencies of the laws: if encryption was banned for export, what would happen to a traveler crossing borders at the airport with this code on a T-shirt? Would they be allowed to board?
Other source codes have also been considered illegal, for example, by certain lobbying groups, and also widely disseminated by Internet users to mock these laws. This was the case with DeCSS, which allows the reading of copyprotected DVDs.
RSA Encryption
RSA encryption – named after its inventors Rivest, Shamir and Adleman – is a cryptography algorithm described in 1977, widely used to transmit confidential information securely over the Internet, for email or the exchange of banking information.
Encryption algorithms were considered to be technologies with both civilian and military uses by the United States government, and thus regulated as such.
BIOGRAPHY
Stéphane Bortzmeyer works at Afnic, the registry for .fr domain names. Specializing in network protocols, he does little programming, mostly practical tools. His favorite programming languages are C, Zig, Go, Python, Elixir, and Haskell. He also enjoys reflecting on the social and political issues raised by computing, and especially the Internet. In 1995, he wrote an op-ed in Le Monde — the first text in France advocating for the liberalization of cryptography.
#Encryption
#Hacking
Additional references
- L’histoire du code RSA en Perl : Adam Back, « The quest for the most diminutive munitions program » http://www.cypherspace.org/rsa/story.html
- « The original post to the cypherpunks list, followed by Hal Finney’s reply where he picks the program apart and explains how it works », Date: 9 Mar 1995 04:06:20 -0500 From: aba@atlas.ex.ac.uk To: cypherpunks@toad.com Subject: perl hackery, export-a-crypt-system http://www.cypherspace.org/rsa/org-post.html
- The T-shirt, now a collector’s item, is available on several resale platforms like eBay https://www.ebay.com/itm/405589746700
- Jonathan Touboul. « Nombres premiers et cryptologie : l’algorithme RSA ». Interstices . 20 décembre 2007 https://interstices.info/nombres-premiers-et-cryptologie-lalgorithme-rsa/
- Anne-Sophie Letellier, « Les Crypto Wars ». À bâbord !. Revue sociale et politique, no 85, automne 2020https://www.ababord.org/Les-Crypto-Wars