Michał “lcamtuf” Zalewski & forgotten contributor, 1998.
After including a similar “fork bomb” in his signature for a while, the computer security expert who first presented this code received an email suggestion to use “:” as a function name, so the concise script would begin with an open-mouthed smiley. This script is now not only sold as merchandise (T-shirts, stickers, mugs, etc.); several people have had it tattooed on themselves.
ABOUT CODE
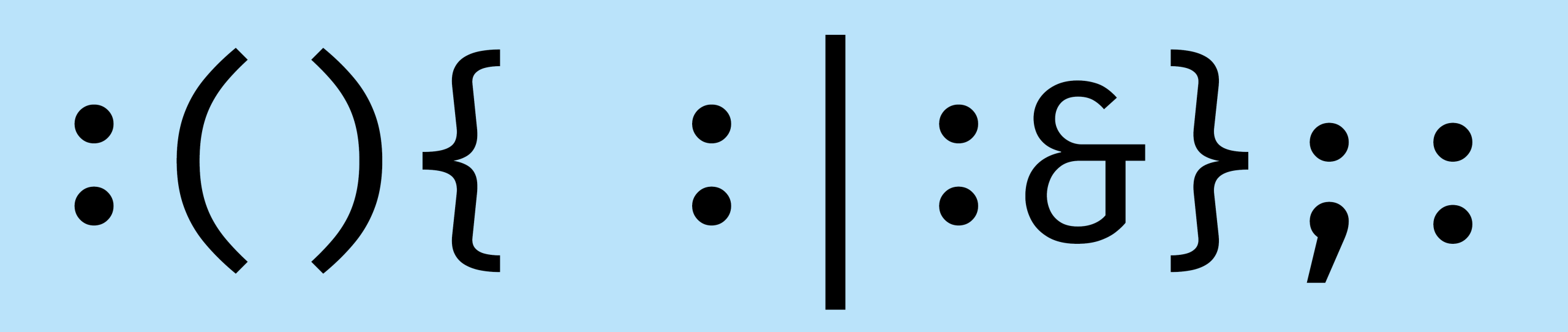
The very short Unix shell script
:(){ :|:& };:
functions the same way as the longer and clearer program
spawn() {
spawn | spawn &
}; spawn
Perhaps the shortest example of malware, this is also an elegant recursive program that has only the “side effect” of slowing, then crashing, the computer.
The longer version begins with a function definition. That function is called “spawn” – the shorter version uses the name “:” instead. When run, this function calls itself once on the left side and – using the pipe symbol “|” – sends any output to another invocation of itself on the right side. So each invocation of the function results in two more invocations. This is all done in the background (indicated by “&”), so the system does not wait for this to complete; it can proceed to do more work. In the final part of the script – after the function definition has concluded with “};” – the function itself is invoked. The result of running this script is that “spawn” will be defined and invoked, which will invoke two further “spawn” processes, each of which will call two more, and so on, and so on. This very short script can bog down a multiuser computer system. It’s also beautiful code that reveals how computer programs can invoke themselves recursively.
While this can be used maliciously on systems that have not defended against it, it probably serves, most of the time, as a sort of riddle for those who are discovering the mysteries of the Unix shell: What does this strange sequence of characters do, and why? This is not the first exhibition of this code. It was discovered by Denis “Jaromil” Roio in 2002, who was intrigued enough to present it as an artwork. In a different sort of showcase, contributors have offered an online repository of fork bombs in many programming languages – no doubt for fun and educational purposes, rather than to allow black-hat hackers to wreak havoc.
BIOGRAPHY
Nick Montfort develops and studies computational poetry and art. He is professor of digital media at MIT and principal investigator in the Center for Digital Narrative at the University of Bergen, Norway. Among his several projects, he co-founded and publishes the magazine Taper for short computational poems, all of them free software. He releases his own creative and research software this way as well.
#Recursion
#Riddles